Understanding the Critical Role of a VPN in Modern Digital Life
In an era where cyber threats are growing, protecting your private data has never been more crucial. A VPN scrambles your digital communications, ensuring that cybercriminals, network administrators, and external entities cannot track your digital footprint. Whether you’re accessing public Wi-Fi at a coffee shop or processing private records, a VPN acts as an digital shield against security leaks.
Many users overlook the threats of unsecured networks, putting at risk their credit card numbers, account details, and chat records. By routing your connection through secure servers, a 快连 conceals your digital location and geolocation, making it extremely difficult for tracking agencies to target you.
Selecting the Ideal VPN for Your System: A Comprehensive Comparison
Selecting the right VPN tool depends on your specific needs and platform. For Windows users, look for user-friendly interfaces, high-speed connections, and rigorous encryption. Apple loyalists should prioritize flawless operation with Apple ecosystems, while Linux aficionados may favor configurable options.
Smartphone users must select VPNs with mobile-optimized applications that reduce energy usage and bandwidth usage. Universal access is key if you often alternate between desktops, tablets, and handsets. Always check that your VPN works with up-to-date technologies like IKEv2 for peak efficiency.
Step-by-Step Guide to Downloading a VPN on PC Systems
Start by, visit the official VPN website using a trusted browser. Identify the get started area and pick the PC-friendly edition. After acquiring the file, launch the executable and follow the step-by-step instructions.
As you install, modify options like automatic startup and protocol selection. Activate the emergency stop feature to prevent breaches if the VPN drops. Lastly, sign in with your account details and link to a server of your choice.
Optimizing VPN Usage on Mac Systems
Apple’s platform delivers native support for VPNs, but specialized tools often provide better functionality. Once you’ve installed, drag the VPN software to your software library. Launch the app and key in your account information to enable the service.
Modify preferences such as encryption standards and server locations. Enable split tunneling to direct certain programs through the 快连手机版 while letting others to use your standard internet. For added protection, integrate your VPN with Firewall tools to block ransomware and scam websites.
Securing Open-Source Platforms with a VPN
Linux users often prefer VPNs that support terminal-based setups. Begin by, updating your system library to guarantee availability to the updated applications. Use CLI instructions to set up the VPN client, adhering to guides provided by your service.
Configure network settings to automate VPN connections during boot-up. Advanced users can embed firewall rules to restrict non-VPN traffic. Frequently inspect records to spot anomalies and patch your VPN software to fix vulnerabilities.
Protecting Smartphones with VPNs on Android and Apple’s Platform
Handheld gadgets are prime targets for cyberattacks due to their constant connectivity. Install your VPN app from the Apple App Store to steer clear of fake apps. Start the app, authenticate, and pick a server geographically proximate for quicker response times.
Activate features like ad-blocking to enhance your online sessions. Adjust the VPN to instantly join when accessing open hotspots. For Apple mobile devotees, activate persistent connection in system preferences to maintain privacy even if the app shuts down.
Advanced VPN Features to Enhance Your Privacy
Today’s services deliver advanced features that go beyond standard protection. A network blocker stops all internet traffic if the VPN drops, avoiding data exposure. Double VPN sends your connection through two or more locations, masking your digital trail even further.
Threat detection systems stop annoying pop-ups and prevent phishing sites. Split tunneling lets you choose which apps use the VPN, prioritizing speed and security. For organizations, fixed locations and account control facilitate encrypted communication.
Addressing Common False Beliefs About VPNs
Despite their widespread use, many users misunderstand how VPNs work. A common fallacy is that VPNs completely hide your digital behavior. While they hide your IP address, browser fingerprints can still leak your details. Additionally, not all VPNs practice strict no-logs policies, so researching your provider’s practices is essential.
A further misconception is that VPNs significantly slow connection rates. While data scrambling creates latency, top-tier tools reduce this impact with high-speed networks. Lastly, more info unpaid tools often sacrifice privacy by sharing user data or serving tracking-based marketing.
Future-Proofing Your Online Presence with a VPN
As cyber threats advance, keeping safe requires forward-thinking steps. New developments like next-gen processing could undermine current protection methods, making it essential to opt for VPNs committed to upgrading their infrastructure. Integrating a VPN with supplementary measures like secure storage and multi-step verification creates a comprehensive defense framework.
Authorities worldwide are strengthening online protection statutes, and a VPN guarantees you align with these requirements. Whether you’re watching videos, engaging in eSports, or conducting business, a VPN remains an crucial tool for navigating the online realm safely.
 Daniel Stern Then & Now!
Daniel Stern Then & Now!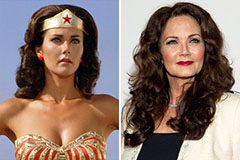 Lynda Carter Then & Now!
Lynda Carter Then & Now! Atticus Shaffer Then & Now!
Atticus Shaffer Then & Now! Jeri Ryan Then & Now!
Jeri Ryan Then & Now! Stephen Hawking Then & Now!
Stephen Hawking Then & Now!